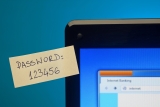
Young workers are more gullible to tech scams
Young workers are more gullible to tech scams, well that is what the latest studies show. The old cold-call scam is still a popular way for fraudsters to dupe people out of their money. But now they’re taking their tactics to the computer generation, and it can be surprising just who is falling for the …